The LucidView Enforcer is an Enhancement for MiKroTik routers:

Intrusion Prevention - Identify/kill Unauthorised remote hacker access
Protect one’s Network from Unauthorised remote Internet access, that is typically used to plant Ransomware, copy/steal data, etc.

Content filter (DNS & Firewall Based)
- Easily selectable Category list of content.
- * Whitelisting and blacklisting of domains, hosts and IPs
- * Time based rules to block or allow between times, for categories, or specific hosts
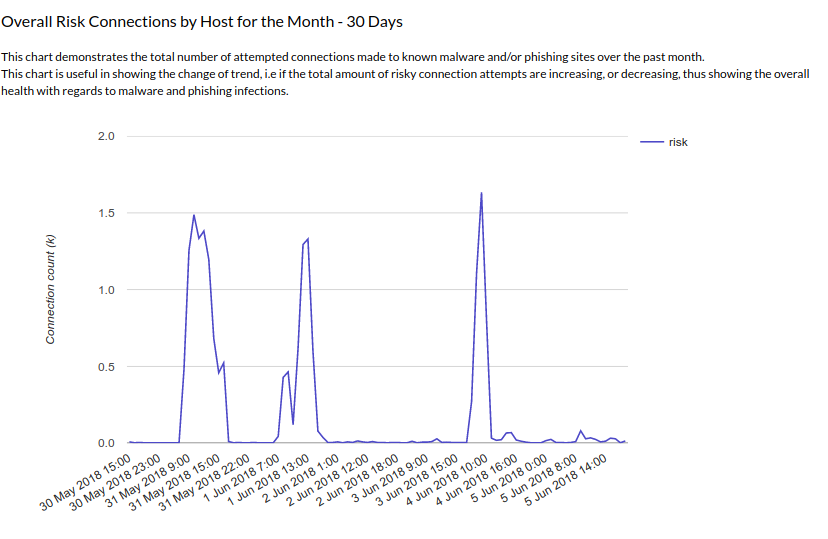
Reports, Dashboards and Traffic-flow Analysis
- Daily, Weekly and/or Monthly usage reports that are emailed out, which are meaningful and human readable. Preset and Custom
- Customisable Dashboards for at-a-glance traffic management and security risk overviews
- Traffic-Flow Analysis providing a deep dive traffic investigation tool to find the proverbial "needle-in-a-haystack".
- Perfect for auditing purposes and log analysis

Saturation Manager
Enable all on the network to have responsive Internet access. Ensure bandwidth is always available for critical applications, even during times of peak usage.
LucidView has developed breakthrough technology that allows complete traffic management on large links ranging from 1Gbps - 100Gbps. This solution is not simply QoS/QoE based but enables Content based traffic shaping.

One central Cloud Core MikroTik Router/VM - Only available on Pro Accounts
- MikroTik Cloud core routers (or Mikrotik virtual machine Images), can be installed centrally, hosting thousands of Enforcer profiles, allowing each of your clients to have their own Enforcer, without actually installing thousands of smaller MikroTik routers. -- Ideal for ISP’s and Large Enterprises.
- Allowing your clients to choose from “pre-set” profiles, instead of full customization of each client.
- Enterprise costing available.

WIFI Access point
The Interface allows for the Management of the SSID name password channel, etc
Central Cloud Core MikroTik Router/VM does require LucidView to have remote access to your MikroTik Routers, and may require time and material service purchase too.